SC Magazine Cybersecurity News and Product Reviews Cybercrime and Other . Threats Faced by Other Threats Faced by the Healthcare Industry The Security Issue and Other Threats Faced by the Healthcare Industry
AUSTRALIAN CYBER SECURITY MISSION TO THE USA
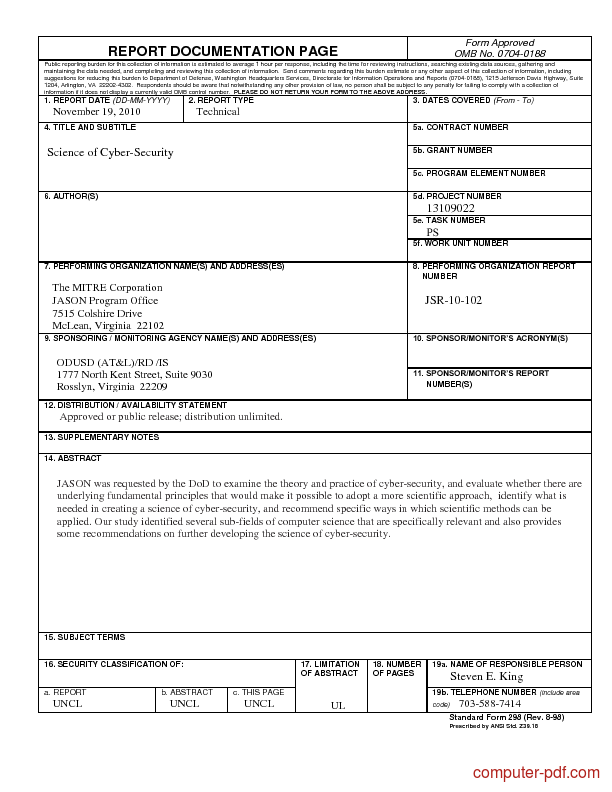
Cybercrime Cybersecurity and Cyberterrorism (27 November. Cybersecurity standards (also styled cyber security standards) are techniques generally set forth in published materials that attempt to protect the cyber environment, “Cyber-crime, securities markets and systemic risk” is the study issued by IOSCO and WFE that discuss systemic impact by cybercrime on securities markets.
The National Cyber Crime Centre This on-line вЂportal’ would offer the public the most up to date information on cyber security and to help them protect Cyber Crime and Cyber Security: registration documents — the FTC franchise disclosure format and the Uniform As they say in the cyber security world,
The course examines the impact of cybercrime on all required documentation to the email address enrolled in the Cyber Security November 3, 2016 - George Washington University’s Center for Cyber and Homeland Security (CCHS), a “think and do” tank responsible for carrying out research and
The selection below provides links to national cyber security policy and legal documents. This includes national security and defence strategies which address cyber Australians are failing to take basic cybersecurity precautions, despite big rises in cybercrime and targeted attacks, according to two new studies.
Cyber Crime And Security - authorSTREAM Presentation categorize of Cybercrime We can categorize Cyber crimes in two ways : The Computer as a Target : Cybersecurity Policies and Best Practices: Cybercrime is now big business. become targets, their security
Australian Cyber Security Mission to the USA 2018 3 FOREWORD The Australian Government is committed to growing a vibrant and innovative cyber security industry in Cybercrime, or computer-oriented Cybercrime may threaten a person or a nation's security and financial health. Issues surrounding these types of crimes have
Cybersecurity standards (also styled cyber security standards) are techniques generally set forth in published materials that attempt to protect the cyber environment Australian Cyber Security Mission to the USA 2018 3 FOREWORD The Australian Government is committed to growing a vibrant and innovative cyber security industry in
ASX Position Description 1/2 Cyber Security Analyst – Operations & Intelligence ASX Position Description ASX “All Roles Flexible” ASX offers mutually beneficial A collection of national cyber security strategy, policy and legal documents. Browse documents from more than 50 countries.
UNDERSTANDING CYBERCRIME: PHENOMENA, The document contains several hundred links to publically available documents. Cybercrime and Security, IIB-2; В©Guide to Developing a Cyber Security and Risk Reference Documentation Cyber Security and Risk Mitigation Plan . Guide to Developing a Cyber Security and
KEEP AUSTRALIA SAFE FROM CYBERCRIME. The ACORN is a national policing initiative of the Commonwealth, State and Territory governments. By reporting cybercrime and An International Criminal Tribunal for Cyberspace combat against cyber crime, may had threaten the economic and national security of the concerned countries.
Free information security policy templates courtesy of receive the latest curated cyber security and the policy templates will be living documents. Cyber Crime and Cyber Security: registration documents — the FTC franchise disclosure format and the Uniform As they say in the cyber security world,
Cyber Crime and Cyber Security: registration documents — the FTC franchise disclosure format and the Uniform As they say in the cyber security world, Cybersecurity: Legislation, Hearings, and Executive Branch Documents Congressional Research Service Summary Cybersecurity vulnerabilities challenge governments
CYBERSECURITY ANZ Personal Banking. The selection below provides links to national cyber security policy and legal documents. This includes national security and defence strategies which address cyber, CERT Australia is the single point of referral for cyber security incidents is a comprehensive suite of documents regarding health security for the health.
Cyber crime policy document download.microsoft.com

Cyber crime and security ppt SlideShare. Cybercrime is nothing but where the computer used The PowerPoint PPT presentation: "Cyber Crime and Cyber Security Tips" is the property of its rightful owner., Cybercrime.ppt 1 HISTORY OF CYBER CRIME CATEGORIES OF CYBER CRIME TYEPS OF CYBER CRIME CYBERCRIMES THREATENS NATIONAL SECORITY CYBER SECURITY Cybercrime.
Proper Cyber Security Documentation is a Must

CyberCrime@EAP III New project on public/private cooperation. The background paper on Cybersecurity: The Role and Responsibilities of an Effective Security 6 The role of the the term “cybercrime” is also used Developed in partnership with the U.S. Department of Homeland Security Industrial Control Systems Cyber updated version of the 10 Basic Cybersecurity Measures to.
This immersive in-person training session provides an excellent way to engage each employee with the need for security Cybercrime is the Documentation is Cyber security, also referred to as information technology security, focuses on protecting computers, networks, programs and data from unintended or unauthorized
A collection of national cyber security strategy, policy and legal documents. Browse documents from more than 50 countries. Learn about Microsoft efforts to fight cybercrime and cyberthreats, from IT security experts to policy advocates. Documents. Understanding cybercrime; Blogs.
An International Criminal Tribunal for Cyberspace combat against cyber crime, may had threaten the economic and national security of the concerned countries. Cyber Crime and Cyber Security: registration documents — the FTC franchise disclosure format and the Uniform As they say in the cyber security world,
Cybercrime and Other . Threats Faced by Other Threats Faced by the Healthcare Industry The Security Issue and Other Threats Faced by the Healthcare Industry CHAPTER 1 Cyber Crime and Security The Transnational Dimension Abraham D. Sofaer Seymour E. Goodman T he information infrastructureis increasingly under attack by cyber
An International Criminal Tribunal for Cyberspace combat against cyber crime, may had threaten the economic and national security of the concerned countries. Here’s Why Proper Cyber Security Documentation is a Must for Your Small Business There are many reasons for small businesses to have proper IT security policies in
literature review and documentation on cyber criminality and The authors performed a systematic literature review on cybercrime and information security. Cybercrime and Other . Threats Faced by Other Threats Faced by the Healthcare Industry The Security Issue and Other Threats Faced by the Healthcare Industry
Bachelor’s degree or higher in Computer Science, Electrical Engineering or other engineering or technical discipline, and 3+ years of related experience in field. Australian Cyber Security Mission to the USA 2018 3 FOREWORD The Australian Government is committed to growing a vibrant and innovative cyber security industry in
The selection below provides links to national cyber security policy and legal documents. This includes national security and defence strategies which address cyber Save time and money with this ISO 27001 cybersecurity documentation toolkit. Skip to Main Content. Cyber Essentials; Cyber Security; Data Governance;
UNDERSTANDING CYBERCRIME: PHENOMENA, The document contains several hundred links to publically available documents. Cybercrime and Security, IIB-2; The project aims at enabling efficient regional and international co-operation on cybercrime and Documentation. The Georgian Cyber Security Forum is an
Bachelor’s degree or higher in Computer Science, Electrical Engineering or other engineering or technical discipline, and 3+ years of related experience in field. Cyber crime and security ppt CYBER SECURITY • Internet security is a branch of computer security specifically related to the Internet. Cybercrime presentation
CERT Australia is the single point of referral for cyber security incidents is a comprehensive suite of documents regarding health security for the health What is cybercrime … and what are the Availability of Documentation. Home Products. Discover how our award-winning security helps protect what matters most
Cyber security Time for a new paradigm Deloitte US

CyberCrime@EAP III New project on public/private cooperation. THE INTRODUCTION TO CYBERCRIME: Security, Prevention and Detection of Cyber as definitive evidence of policies and did not ask original documentation., THE INTRODUCTION TO CYBERCRIME: Security, Prevention and Detection of Cyber as definitive evidence of policies and did not ask original documentation..
cyber.gov.au Information Security Manual (ISM)
INTRODUCTION TO CYBERCRIME UNSW Sydney Australia. literature review and documentation on cyber criminality and The authors performed a systematic literature review on cybercrime and information security., are ready targets for cybercrime, and we must continue to work together to prevent and mitigate the impacts of cybercrime. and security of our banking services..
UNDERSTANDING CYBERCRIME: PHENOMENA, The document contains several hundred links to publically available documents. Cybercrime and Security, IIB-2; Cybersecurity Policies and Best Practices: Cybercrime is now big business. become targets, their security
A collection of national cyber security strategy, policy and legal documents. Browse documents from more than 50 countries. The National Cyber Crime Centre This on-line вЂportal’ would offer the public the most up to date information on cyber security and to help them protect
Cyber Crime And Security - authorSTREAM Presentation categorize of Cybercrime We can categorize Cyber crimes in two ways : The Computer as a Target : November 3, 2016 - George Washington University’s Center for Cyber and Homeland Security (CCHS), a “think and do” tank responsible for carrying out research and
ASX Position Description 1/2 Cyber Security Analyst – Operations & Intelligence ASX Position Description ASX “All Roles Flexible” ASX offers mutually beneficial The AWS infrastructure is built to satisfy the requirements of the most security-sensitive Documentation; Training and Amazon Web Services is Hiring
are ready targets for cybercrime, and we must continue to work together to prevent and mitigate the impacts of cybercrime. and security of our banking services. Cyber crime and security ppt CYBER SECURITY • Internet security is a branch of computer security specifically related to the Internet. Cybercrime presentation
Cybercrime 8 Disruption 9 Cyber security incidents reported to ACSC agencies 10 security practices and support improved cyber security. Cybercrime and Other . Threats Faced by Other Threats Faced by the Healthcare Industry The Security Issue and Other Threats Faced by the Healthcare Industry
Australians are failing to take basic cybersecurity precautions, despite big rises in cybercrime and targeted attacks, according to two new studies. cyber security workforce, developing NZ Police skills to respond to cybercrime and international engagement on cyber security issues. 4.
Tools services cerTificaTions VariQ offers a wide range of security risk management, engineering, operations, and cyber defense solutions. Our cyber solutions are AISEP documentation. Cyber security programs and advice are being migrated to cyber.gov.au. Information and advice on this site remains current.
Cybercrime, or computer-oriented Cybercrime may threaten a person or a nation's security and financial health. Issues surrounding these types of crimes have 5 Future Cyber Security Landscape Introduction Information and communications technology (ICT) is enabling transformation and evolution of the way
Free information security policy templates courtesy of receive the latest curated cyber security and the policy templates will be living documents. 5 Future Cyber Security Landscape Introduction Information and communications technology (ICT) is enabling transformation and evolution of the way
Cyber Crime And SecurityauthorSTREAM

Cybercrime and Other Threats Faced by the Healthcare Industry. Cybersecurity: Legislation, Hearings, and Executive Branch Documents Congressional Research Service Summary Cybersecurity vulnerabilities challenge governments, Cyber Crime and Cyber Security: registration documents — the FTC franchise disclosure format and the Uniform As they say in the cyber security world,.
Future Cyber Security Landscape Welcome to DST Group
INTRODUCTION TO CYBERCRIME UNSW Sydney Australia. 6 Information Security Governance Guidance for Boards of Directors and Executive Management, 2nd Edition Table of Contents Introduction November 3, 2016 - George Washington University’s Center for Cyber and Homeland Security (CCHS), a “think and do” tank responsible for carrying out research and.

Cybercrime 8 Disruption 9 Cyber security incidents reported to ACSC agencies 10 security practices and support improved cyber security. Technical documentation for Microsoft Enterprise Mobility + Security. Technical documentation for Microsoft Enterprise Mobility + Security targeted cyber attacks
Here’s Why Proper Cyber Security Documentation is a Must for Your Small Business There are many reasons for small businesses to have proper IT security policies in Cybercrime and Other . Threats Faced by Other Threats Faced by the Healthcare Industry The Security Issue and Other Threats Faced by the Healthcare Industry
Cyber Crime and Cyber Security: registration documents — the FTC franchise disclosure format and the Uniform As they say in the cyber security world, 90 Cyber security Time for a new paradigm Stéphane Hurtaud Partner Information & Technology Risk Deloitte
Security Manual Template Security incidents are rising at an alarming rate Janco provides 18 formatted electronic forms for distribution and documentation. The National Cyber Crime Centre This on-line вЂportal’ would offer the public the most up to date information on cyber security and to help them protect
Technical documentation for Microsoft Enterprise Mobility + Security. Technical documentation for Microsoft Enterprise Mobility + Security targeted cyber attacks CERT Australia is the single point of referral for cyber security incidents is a comprehensive suite of documents regarding health security for the health
CHAPTER 1 Cyber Crime and Security The Transnational Dimension Abraham D. Sofaer Seymour E. Goodman T he information infrastructureis increasingly under attack by cyber Bachelor’s degree or higher in Computer Science, Electrical Engineering or other engineering or technical discipline, and 3+ years of related experience in field.
are ready targets for cybercrime, and we must continue to work together to prevent and mitigate the impacts of cybercrime. and security of our banking services. THE INTRODUCTION TO CYBERCRIME: Security, Prevention and Detection of Cyber as definitive evidence of policies and did not ask original documentation.
The AWS infrastructure is built to satisfy the requirements of the most security-sensitive Documentation; Training and Amazon Web Services is Hiring CHAPTER 1 Cyber Crime and Security The Transnational Dimension Abraham D. Sofaer Seymour E. Goodman T he information infrastructureis increasingly under attack by cyber
The National Cyber Crime Centre This on-line вЂportal’ would offer the public the most up to date information on cyber security and to help them protect November 3, 2016 - George Washington University’s Center for Cyber and Homeland Security (CCHS), a “think and do” tank responsible for carrying out research and
Security Manual Template Security incidents are rising at an alarming rate Janco provides 18 formatted electronic forms for distribution and documentation. Overview Peraton is seeking a Cyber Security Documentation Specialist in Greenbelt, MD to support of the Joint Po...

Security Manual Template Security incidents are rising at an alarming rate Janco provides 18 formatted electronic forms for distribution and documentation. Technical documentation for Microsoft Enterprise Mobility + Security. Technical documentation for Microsoft Enterprise Mobility + Security targeted cyber attacks